In 2022, everything is digitalized, right from the business, corporates, education, governments, and even socialization. IT is valuable and we are quite dependent on it, thus it keeps evolving and growing according to the latest trends and market. This constant technological change comes with both- advantages and disadvantages. It can be compromised anyway. Technological risks can cause various kinds of damage- financial, reputational, and informational disrupting the security and performance. There can be software as well as hardware risks involved. One should always use technology with utter care and responsibility.
Here are the top ten technological risks in 2022 that you need to be aware of.
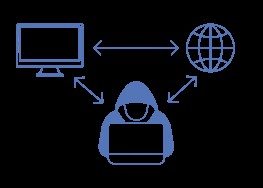
1. Phishing
It means when the hackers trick the receivers to reveal their credit/debit card numbers, OTPs, or any login information to extract money from their bank accounts. They also ask users to open links sent through emails and SMS from companies that look legitimate. One should never share such information and always confirm with your bank about the same.
2. Cloud System
When company stores and accesses your data in their computing system, it is called cloud computing. It is usually used for ad suggestions and future notifications. They save data like login ids and passwords etc. Although big companies usually have a well-equipped security net, there still lies a chance of data leaks.
3. Hardware Failures
There is always a chance of physical and technical mistakes as a form of human error. For example, using old devices (old broadbands, old telephones) can cause a hurdle in the world of new technological trends. These devices can’t keep up with the latest updates and thus can corrupt or cause loss of data.
4. Malicious Attacks
Malware (malicious software) disrupts your computer operations. Viruses, ransomware, spyware, and trojans are different types of malware. These ransomware attacks the data in your devices causing them to corrupt or lose permanently. They can also cause damage to your hardware devices and break down your computer networks.
5. Man in the Middle
MITM attacks mean when a perpetrator places himself between a user and the application they are using. They hijack, retain information, and disrupt the flow of communication between them. They can go undetected until it’s too late. This usually occurs on eCommerce websites. To prevent such attacks, avoid using unprotected WIFIs or public networks.
6. Drive-by attacks
In such a kind of attack, the cybercriminals plat their script in unprotected codes of web pages. They are called drive-by attacks because the user need not click on any link for the attack, simply visiting the website also causes the cyber-attack. To avoid it, one should always use recent versions of apps and software and visit the most updated websites.
7. Operational Risks
It is a type of risk where companies can suffer great loss due to flawed operations or system failures and incorrect data. It can also happen because of human errors while using the systems. They can cause a company to lose its credibility as well as incur a monetary loss.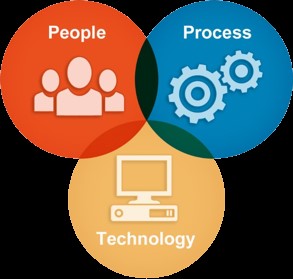
8. Cryptocurrency
Many crypto thefts cause the loss of digital money. Lack of regulations and easy to breach websites are the key reasons for such practices. As these cryptos are stored in digital wallets that are usually some kinds of websites or apps, there is always a chance of hackers phishing these sites.
9. Botnets
They are a collection of various internet-connected devices that are attacked and controlled by some type of malware with an unknown owner. They are usually found spamming social media posts. They even send out spam messages and emails that may lead to extortion of money and access to private information.
10. Webcam Hacking
Cyber hackers can also take over your hardware devices such as a web camera. They can look at and record audio and videos through your device and even access these files. Webcams are used to extort money and personal information. Avoid suspicious links, unplug your camera when not required, and keep changing passwords as a precaution for the same.