In this topic, we are going to discuss the top 10 security trends, especially cyber security trends, being followed in 2018. The center part of this is to reveal how serious security has become these days.
1. Privacy regulation and Data Protection

The data of Cambridge Analytica revealed that in 2018 alone the social media giant Facebook’s about 2.2 million users experienced malicious scrapers in their accounts. The activated search feature led the hackers to decode the full names of persons associated with a particular e-mail or even phone number. Now to counter this, the open search facility has been disabled also the third party apps are restricted to access user’s information regarding personal details.
2. Artificial Intelligence measures on the rise
Cyber-attacks can be effectively battled with the help of artificial intelligence and machine learning. By using AI-based authentication technique and algorithms of machine learning, a robust user profile can be created that is way more secure from attacks. The use of AI and machine learning in the era of Big Data is the best way available to assess large amounts of data and is a great step to top cyber hackers to gain access into the confidential user data.
3. Biometric Authentication
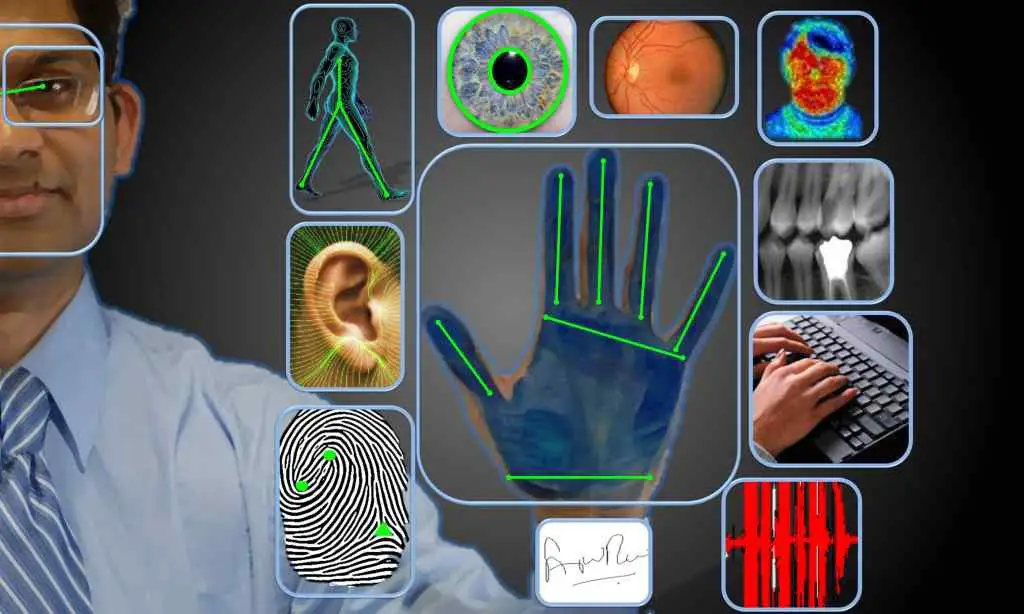
Improved methods of biometric authentication methods have come into the scene after Apple launched FaceID. The flawless FaceID technology and biometric authentication make it easy and attractive for users to leave behind the password driven security which was way easier to breach. The funny thing is if the thief physically steals the phone with face id or fingerprint then he will easily be able to gain access the data by unlocking it.
4. The rate of attacks on the IoT (Internet of Things) devices has increased

From keyless entry to homes and offices to medical devices and printers, IoT gadgets are almost everywhere. The trend to be followed is the makers of IoT devices should provide built-in security features and the authorization method required to gain access to this device must be hardcore.
5. The attempt of Healthcare industries to protect or safeguard themselves from cyber threats

The health-related data is of a great value to the hackers on the dark web and the attacks are on a constant rise from the past few years. Increased ransomware attacks and hacking of the MRI machines and the printers used has really posed a threat. A secure and nicely encrypted login system should be provided for these devices as well.
6. Ransomware attacks on the increase
Everyone knows about the most infamous ransomware namely WannaCry. It is one of the examples of the outbreaks that aimed at various industries forcing the companies to reconsider the security systems. It is necessary for all sorts of companies to consider the high level of security so that they could be saved fro the vicious circle of cyber attacks. We should never fall prey to the fake links present in spam emails also we should ignore fraudulent SMSes that we receive.
7. Smart Manufacturing to be protected from cyber attacks

The production of equipment and products by making use of smart manufacturing is revolutionizing various industries. The manufacturing environments are made without considering cyber security. These devices come under the commercial IoT devices. A serious investment should be made in providing the best security available like a necessary login password which should have high requirements.
8. CryptoCurrencies under attack

Many Cryptocurrency providers along with Bitcoin are enabling dad and mom, investors and individuals, to manage finances online with the help of this provision. The security guidelines are very limited in the exchange though it has been improved in the past few years, the flaws have made these systems more vulnerable to hackers. The needs are on rise where more secure ways are needed to access cryptocurrencies on the web.
9. Redesigning PII(Personally Identifiable Information) and Data Minimization
Customer’s Personally Identifiable Information for authentication is like water for the thirsty for the hackers. This data is difficult to protect so it is easily viewed by online thieves. Methods like security compliance , and data loss prevention methods are the latest technology trends in cyber security.
10. Job Titles for ethical hackers in Demand

A recent Talk Talk data breach has led as an outcome the birth of a new job title which is of a CCO(Chief Cyber crime Officer) whose duty will be to protect computer systems regularly and online platforms from cyber-attacks new technologies getting discovered every minute of the day the security threats also increase side by side.