Every cyber-security issue arises commonly through the use of external devices, sharing passwords, locating other unnecessary networks, etc. If you are a professional, then without knowledge about data security, you may ruin your life from working carelessly in an office setup, damaging the company’s name. Thus, the following ten tips may help in getting into a cyber-safe environment with technology.
1. RISK MANAGEMENT REGIME

A risk management regime helps an organization to understand the risks they face before the implementation of the security measures. You can request the security systems to change or add the policies according to your staff awareness.
2. HOME AND MOBILE NETWORKING

Many offices and organizations now offer employees to work from home. But this may have some security risks like remote workers who will not get the network security that is available from the office. So, the offices should be responsible for creating policies to protect devices which the employees are using.
3. MALWARE PROTECTION

There are several types of malware that affect an organization’s system. The virus can be seen even from sending an email, or by removable devices that were plugged into computers. There are many anti-malware to protect employees from risks.
4. MONITORING
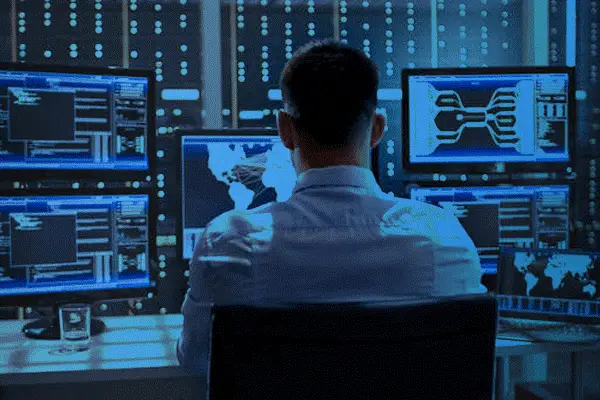
System monitoring helps an organization to identify incidents promptly and take immediate response. Also, system monitoring will help in making effectual decisions at the right time through the data and analysis made.
5. REMOVABLE MEDIA CONTROLS Removable devices like USB may be one of the reasons for security problems. System users anywhere should not allow a third person to plug removable devices into your systems without proper security policies.
Removable devices like USB may be one of the reasons for security problems. System users anywhere should not allow a third person to plug removable devices into your systems without proper security policies.
6. SECURE CONFIGURATION One of the most common cyber-security issues are configuration not in control and also not updating the software. For reducing the problems of vulnerability through improper machine installation or building network resources, it is to be resourcefully materialized through a proper knowledge about cyber-security and other safety practices.
One of the most common cyber-security issues are configuration not in control and also not updating the software. For reducing the problems of vulnerability through improper machine installation or building network resources, it is to be resourcefully materialized through a proper knowledge about cyber-security and other safety practices.
7. INCIDENT MANAGEMENT
Incident management-IM has the purpose of restoring data of regular service as quickly as possible. It will reduce the adverse effects upon the business management and other operations. It may support you when establishing policies and procedures, strive against damage, and get back up as soon as possible. You can use the method of IM to escalate and diagnose management activities.
8. MANAGING USER PRIVILEGE

Managing privilege helps the employees of an organization to access relevant content to their jobs. Managing systems ensure that every candidate’s profile is safe and nobody can operate or access it without the office’s permissions. Even the employees cannot steal any information from a company.
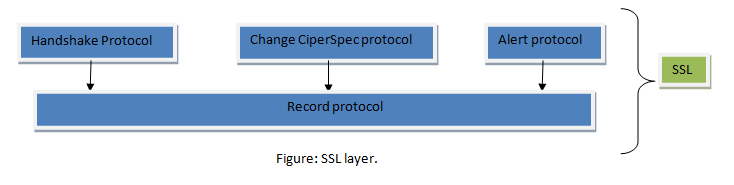
9. NETWORK SECURITY

The internet connection of your system will have vulnerabilities for different malware. You can prevent them by changing the architectural techniques. You must access the policies and other technical measures properly through a secured network system for eradicating the issues of virus attack.
10. USER EDUCATION AND AWARENESS If a user is working in an organization, then he or she should learn how to prevent data from stealing. As a general person, you can try getting into e-learning platforms and other certificate-courses to understand the nooks of cyber-theft and cyber-security. Educating yourself may even help you to be careful while working in your office systems.
If a user is working in an organization, then he or she should learn how to prevent data from stealing. As a general person, you can try getting into e-learning platforms and other certificate-courses to understand the nooks of cyber-theft and cyber-security. Educating yourself may even help you to be careful while working in your office systems.