Do You Know Computer Encryption?
As you go on with your business, searching the internet, downloading your files or just surfing the web, you will come across unsafe and hazardous sites handled by people with malicious intent. Information like your credit card numbers, Social Security number, and passwords gets stored. If not for our network security advances, our important documents and passwords online would be unsafe and prone to stealing.

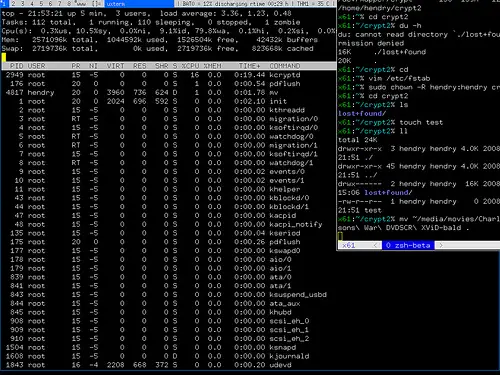
Cryptology, the one that is responsible for developing encryption methods to secure our information online. It stores our information in an area and uses a special kind of key to unlock it. This key I'm speaking of is an Algorithm. Algorithms are a series of numbers with a certain kind of formula to solve and unlock information. Encryption translates our information and turn into binary or a number system that needs a specific algorithm for it to actually make sense.
There are basically two types of Encryption: The symmetric-key encryption and the public-key encryption. Symmetric-key encryption is based on an algorithm that is so sophisticated to protect information stored inside the computers. Using the AES or the Advanced Encryption Standard that uses over 250 codes for small piece of information no matter what it is. Someone who would want to illegally access your files would need to try millions and millions of combinations before knowing a just part of the encrypted password.
The public-key encryption is developed for the use of protecting information on the way to its destination, like a bodyguard for an Armored Van. This uses an asymmetric-key code which is made of two different keys. One key is Private, which is used on an individual computer. The other key is Public, which is shared between the two computers that are sharing the information. The information will be coded first and will be sent with an extra code packet, which is the Public key. The information will then be deciphered using the Public key, but you need to use the Private key to translate it to something that is useable.
Businesses, Web servers, and browsers need different kinds of encryption methods to prevent them and their users any unauthorized access to their valuable information. Numerous protocols are followed on large businesses that need a lot more encryption than a standard personal computer. Whenever a transaction is made online, your browser uses the SSL protocol or the Secure Sockets Layer protocol when sending information.
It is made specifically to any information passed between the Web Servers and browsers. Some more advanced protocols like the Transport Layer Security (TLS) and the usage of digital certificates to identify users are given the special keys so that they can safely exchange valuable information online.