Network Access Protection in Windows 2008
Win Server 2008’s new characteristics have obtained many press reviews, especially the large-scale, glamorous characteristics like Hyper-V and Windows Power Shell. Still, one of the more unseen new security characteristics, Network Access Protection (NAP), is worth some of your time.
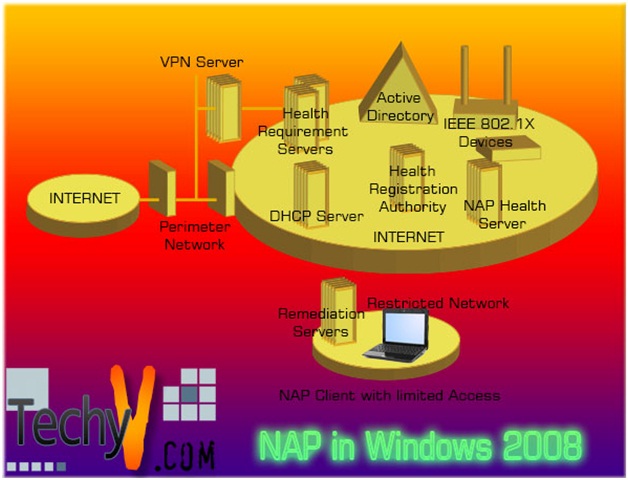
NAP encompasses the newest antivirus programs, patches and so forth. Computers that don’t have rendezvous security measures can be ostracized solely or permitted to only a restricted set of connectivity.
NAP assists and double-checks that computers on the mesh are less probable to be contaminated with and disperse malware. It was initially proposed to be a Windows Server 2003 characteristic, but it took a while for Microsoft to make it work well; sufficient to both, and it’s now here in Windows Server 2008.
With Network Access Protection, system managers of an organization’s computer mesh can characterize principles for scheme health requirements. Examples of scheme health obligations are if the computer has the most latest functioning scheme revisions established, if the computer has the newest type of the anti-virus programs signature, or if the computer has a host-based firewall established and enabled. Connecting or broadcasting computers have their health rank evaluated.
Similarly, computers that obey the system health obligations have full access to the network. Administrators can configure this health principle that makes it likely to double-check that computers not in compliance with scheme health obligations have constrained access to the network.
NAP server can use a health obligation server to validate the health state of the NAP purchaser or to work out the present type of programs or revisions that require to be established on the NAP client. For demonstration, a health obligation server might pathway the newest type of an antivirus signature file. If the NAP enforcement issue is an HRA, it gets health credentials from a certification authority for NAP purchasers that are very resolute to be compliant with health requirements.
If the NAP purchaser is very resolute to be a noncompliant with health obligations, it can optionally be put on a constrained network. The constrained mesh is an ordered subset of the intranet and comprises assets that permit a noncompliant NAP purchaser to correct its scheme health. Servers that comprise scheme health constituents or revisions are renowned as remediation servers.
A noncompliant NAP purchaser on the constrained mesh can get access to remediation servers and establish the essential constituents and updates. After remediation is complete, the NAP purchaser can present a new health evaluation in conjunction with a new demand for mesh to get access or communication.
What’s new that motivates us to use it
These characteristics supply larger flexibility and ease for managers that are organizing a NAP infrastructure. The next parts recount how you can use these improvements.
Multi-configuration SHV
SHVs characterize configuration obligations for computers that try to attach to your network. For demonstration, you can configure the WSHV in order of your need for some or all of the following to be endowed on NAP-purchaser computers:
1. Virus security. If chosen, the purchaser computer should keep an anti-virus submission turned on and established and listed with Windows Security Center.
2. Firewall. If chosen, the purchaser computer should have a firewall that is listed with Windows Security Center and endowed for all mesh connections.
3. Spyware security. If chosen, the purchaser computer should keep an anti-spyware submission turned on and established and listed with Windows Security Center.
4. Antivirus is advanced. If chosen, the purchaser computer can furthermore be tested to double-check that it has the latest antivirus signature document.
5. Automatic upgrade. If chosen, the purchaser computer should be set to ascertain for revisions through Windows renovation program. Also, you can select if you want to download and establish them.
6. Security revisions protection. If chosen, the purchaser computer should have security revisions established and founded on 1 of the 4 security severity rankings in the ‘MS Security Response Center or MSRC.’ The purchaser should furthermore ascertain for these revisions by utilizing a particular span of time. You can employ or select to utilize Win Update, Win Server Update Services (WSUS), or the both to get security updates.
When the SHV carries more than one setting, the SHV characteristic and distinct backgrounds can be retained in more than one SHV setting portfolios. When setting a health principle, you can select the type of SHV you will be utilizing, and made-to-order backgrounds for the SHV if you have set them. For demonstration, utilizing this characteristic, you might conceive the next two health principle settings:
- Default setting. The purchaser computer should carry a Win Update and firewall endowed, anti-spyware & anti-virus submissions should be turned on and upgrade as well as the entire significant security revisions should be ensconced.
- Trusted setting. The purchaser computer should keep an anti-virus submission turned on and upgraded. You can employ these backgrounds in order to conceive health principles whether needing the trusted settings or branded setting backgrounds. Also, you can conceive as numerous exclusive configuration backgrounds as you want.
a. What works differently?
Multi-configuration SHV sways the methods utilized to configure SHVs and health policies. SHV configuration is split into backgrounds configuration and mistake ciphers configuration. If an SHV carries multi-configuration SHV, then added backgrounds can be conceived by right-clicking Settings, selecting New, and then supplying an amicable title for the new configuration.
b. Why is this change important?
It was essential to employ a distinct NAP health principle server to identify a distinct anthology of settings for the identical SHV before. By means of more than one settings of SHV, you can utilize a lone ‘NAP health principle server’ to establish more than one setting of an identical SHV.
c. NAP purchaser client interface improvements
The end client “know-how” has been increased by advancing notes the end users sees about NAP and by incorporating the NAP purchaser client interface into the Action Center on computers running Windows 7. The Action Center presents a centered position to outlook alerts and takes activities that can assist or hold Windows running smoothly.
d. How should I arrange for this change?
Review the NAP principle configuration and backgrounds on all NAP health principle servers on your mesh, so as to work out how they will be influenced by this feature. If you improved these servers from Windows Server® 2008 to Windows Server 2008 R2, verify that all SHV backgrounds are rightly migrated to Default Configuration backgrounds for all established SHVs.
e. Why is this change important?
By incorporating NAP purchaser notifications with the Action Center, the end clienthas a comprehensive outlook of all significant security and upkeep backgrounds on their computer that might require attention.
f. How should I arrange for this change?
Review the kinds of notes supplied by the Action Center on computers running on Windows 7. For demonstration, a red piece in Action Center shows a significant topic that should be addressed soon. Yellow pieces are proposed jobs. For example, upkeep of tasks.
g. What works differently?
When backgrounds or services on an end user’s computer don’ manage rendezvous mesh obligations, the end client might obtain a NAP notification message. These notes have been advanced and incorporated into the Action Center on computers running on Windows 7.