Archive
Must Know About ODBC & DCOM
ODBC (Open Database Connectivity) is Microsoft's answers in favor of processing database in a variety of their programming languages. ODBC is a poor optional (non-object oriented) API for processing database. Open Database Connectivity supports the same application interface for processing database management systems (DBMS). Designers aimed to make it a sovereign of database systems, programming language, and OS. There is no Java corresponding to ODBC.Network Speed Test and Tweaks
In today’s world, information technology is moving faster than your imagination. Many organizations and businesses embraced information technology because of the benefits that the technologies provided for these organizations. One of the most important information technology concepts to any organization is networking. Networking enables organizations achieved many things while combining their ICT resources in one place. Networks enable organizations’ personnel to share resources thus reducing the cost of acquiring such devices/resources. The networks also helps organizations in sharing communication and making the process of communication easier, faster and more effective. Networks enable these business organizations... Read moreBasic PHP
Introduction PHP, which stands for PHP: Hypertext Preprocessor. It was created by Rasmus Lerdorf in 1995 and originally expanded to Personal Home Page Tools. It was renamed to its current recursive form in version 3.0 when released in June 1998. Now , just the acronym PHP itself is widely known.
SQL Server: From the Past to the Future
The SQL Server was originally a joint project between, Microsoft, Sybase, and Ashton-Tate. In 1995, they parted ways and version 6.0 was the first edition released without input from Sybase. From version 7 onwards, Microsoft has rewritten the code, so as not to have to credit Sybase any longer, and be able to drop the Sybase copyright notices; which previously had to be included as an indication of its origin.
MS Groove
Introduction: MS Groove is a desktop application which is used for document collaborations. However, now it is renamed as M.S SharePoint Workspace. It is an offline virtual workspace which allows the users to work remotely but logically integrated in a team. It is very useful for team work, document sharing and for other official purposes. Users can use it while offline.
Mozilla Firefox Top 5 Add-ons
If you are looking for a quicker, more secure, and fully customizable way to surf the web, then your browser of choice is Mozilla Firefox. With its unique features like open source, powerful extension system (more than 1,200 add-ons and counting), themes, OS independent, better support for file formats, better security, 60+ language support, no validation on upgrades, etc. Better still, it stands out from other browsers.
Microsoft Security Essentials review
MSE which is an abbreviation of Microsoft Security Essentials, is an antivirus application launched by Microsoft Corporation. It is helpful in providing protection against all kinds of malware such as Trojan horses, root kits, spyware, and numerous others for Windows® XP, Windows® Vista and Windows® 7 operating systems.
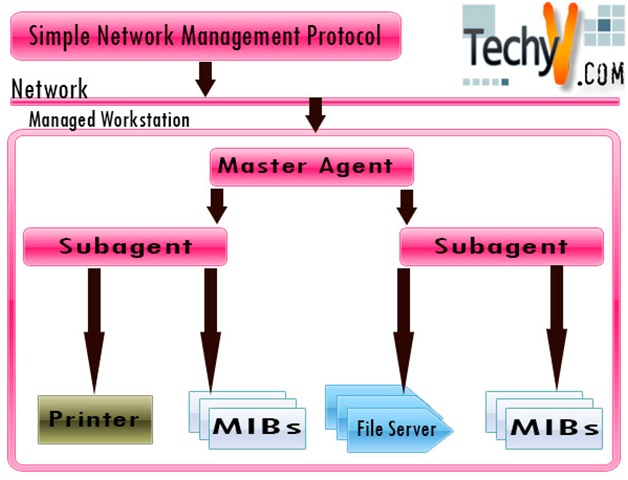
SNMP: Simple Network Management Protocol
Introduction What does Network Management mean? If you have a network of computers, hardware devices like switches, routers, database servers and workstations, surely you will have to:- Keep track of the settings of each device and its functioning.
- Check whether the network is running smoothly and if it can handle the current workload.
- Deal with problems and emergencies in the network.
Microsoft Publisher
Definition: As the name suggests and hints about the application from the marketing world. MS Publishers a DTP application from Microsoft created which proves to be a big challenge and an option for some of the applications like Adobe and QuarkXPress.
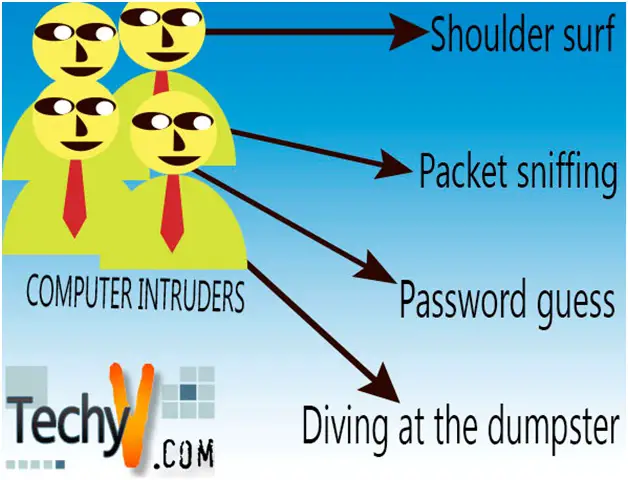
COMPUTER INTRUDERS
Computers are among the most sophisticated machines around the globe; moreover, they carry very important and vital information. This vital information needs to be secured from both external and internal attacks. Many people go extra mile to secure their computers using different techniques and methods including passwords, firewalls, and centralized administration of their resources.