COMPUTER INTRUDERS
Computers are among the most sophisticated machines around the globe; moreover, they carry very important and vital information. This vital information needs to be secured from both external and internal attacks. Many people go extra mile to secure their computers using different techniques and methods including passwords, firewalls, and centralized administration of their resources.
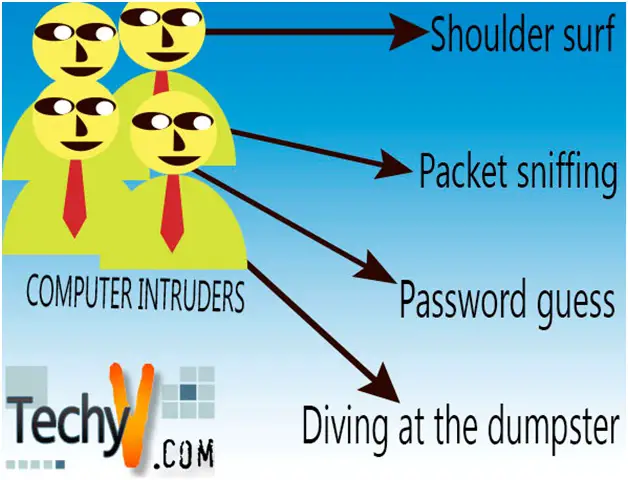
The attacks may consist of viruses; which are malicious programs created by people or even generating themselves. Attacks may also consist of malicious people who may want to destroy documents or acquire documents from your computer. Some people may want to acquire money illegally from people’s accounts, which mostly occurs from the banks. These kinds of people are referred to as computer intruders. There are various ways which intruders may get access to personal computers or even computers belonging to a particular company or firm. Passwords, being the most common way of gaining security, have a number of problems associated with them since people have come up with a number of techniques to get past passwords. These techniques include:
Password guess
A majority of people using computer have passwords which are less complex or even use their names to secure their computer. These kinds of passwords can be guessed, especially by those people who have little knowledge about them. Some people even use the name of their spouses, names of celebrities that they like, their date of birth, and other funny words that they like to use or hear. Most computer intruders are very much literate and have full knowledge about these simple factors. And with little effort, they can guess your password. The best passwords should be a combination of several numbers, words, and even complex symbols.
Shoulder surf
Shoulder surfing is yet another method used by computer intruders. However this practice is usually performed in places which are crowded; including ATM in banks, cyber cafes, and even computer laboratories. With the power of eyes, intruders peep over your shoulder, looking at your hand movement or even what you are typing on the keyboard. With this idea, he can be able obtain your security information, in this case maybe your password on an important information, or PIN for your ATM. Many cyber cafes and banks today have constructed seclusion in performing these operations with only one user at a time to keep away intruders.
Diving at the dumpster
A number of companies dispose people’s and company’s credential unknowingly. These credentials may include important information concerning their usernames as well as password to their documents and files. Dumpster diving method can be used by computer intruders to acquire information that can get them through the network of computers in a given organization. Companies are so advised to discard their litter far from computer intruders or even burn them.
Packet sniffing
This is a technique used by computer intruders in finding traffic within a given network by the use of an application referred to as packets sniffer. The application goes through the stream of data looking for numbers on credit cards, user passwords and important information in the network. Apart from sniffing, the software can also retrieve data and information from the system.
Putting these factors into consideration we can keep our information safe from computer intruders.