Ethical Hacking and its Difference to Malicious Hacking
Ethical Hacking is also often termed as Intrusion, Penetration Testing, Tiger Teaming, Sneaking, or Red Teaming. The methodologies used for ethical hacking are similar to those used for malicious hacking. The only difference between the two is the former uses the methods to report problem, the latter uses them to reap profits illegitimately.

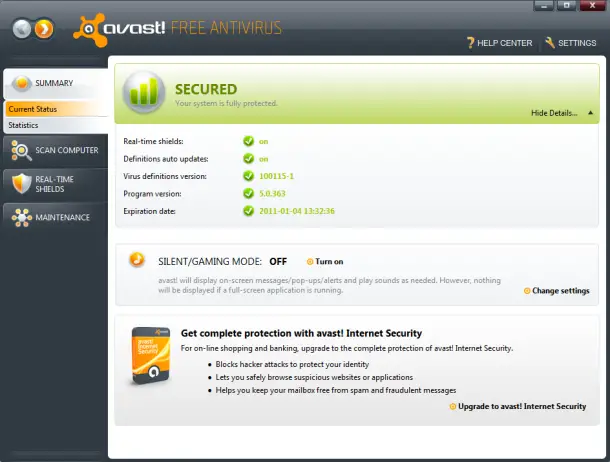
The security experts or the white-hat hackers usually employ methods and several tactics of social engineering to carry out various tests for penetration testing and vulnerability assessment. The commonest hacking tool used by ethical hackers is the MetaSpoilt. Ethical hacking is, thus, an act of using one’s programming skills to identify and evaluate vulnerabilities introduced by malevolent hackers into the computer networks.
Example: One among the earliest instances of ethical hacking is when in the 1970s, the US government made ‘red teams’, groups of security experts, and made them hack into its own systems. Today, big IT giants, like IBM, also maintain their own internal team of ethical hackers. Steve Wozniak and Steve Jobs hacked into Apple Computer and it was a good instance of ethical hacking.
How is an Ethical Hacker Different from a Malicious Hacker (Attacker) – Black Hats Vs White Hats
The exact meaning of the term ‘hacker’ has always been a debatable issue. The hacker may be a person who hacks into an unauthorized system illegally with a negative intention and also someone who does it merely to pursue his/her keen interest in computer technology. To differentiate among the two types of hackers, the word ‘attacker’ is often used to appropriately describe a malevolent hacker. In the common terminology, the attackers are usually referred to as ‘Black hats’, while the ‘security analysts’ or those who do hacking for administrative purposes are referred to as the ‘White Hats’.
However, these terms must not be confused with a "hacktivist", who are mainly involved in identifying and reporting the major security vulnerabilities as means of social activism. The White Hats, who focus mainly on protecting and securing the IT systems, are IT security experts and are commonly called the ‘Ethical Hackers’. The act of attacking/hacking a particular security system to identify various vulnerabilities for the benefit of the system owners is termed as ‘Ethical Hacking’.