In simple words, reverse engineering can be defined as the process of breaking down something to understand it and then build its copy with improved features. This concept applies widely to software codes and databases. In the ethical hacking field, it is applied while identifying the details of a breach that a hacker managed to enter the system and how much harm did he/she cause.
Cyber criminals who are skilled, organized and sometimes well-funded also, utilize a wide range of techniques to harm a system with different objectives. In such a case reverse engineering tools help to identify these techniques so that such attacks don’t take place again in the near future.
This article mentions the top 10 such reverse engineering tools.
1) OllyDbg
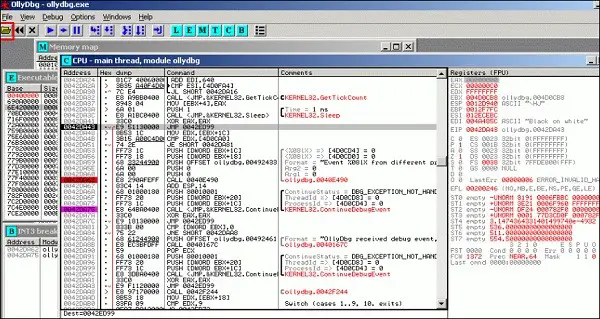
This tool is a 32-bit assembly debugging tool for Microsoft Windows. It analyses the binary codes and is a useful tool if the source code is not available. Although shareware, it can also be used for free. It is known for its ability to locate routines from libraries and object files & directly loads the DLLs for debugging.
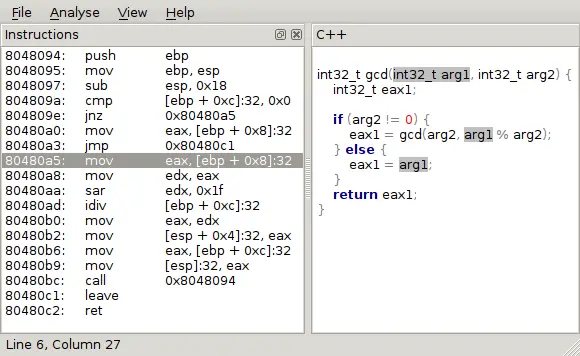
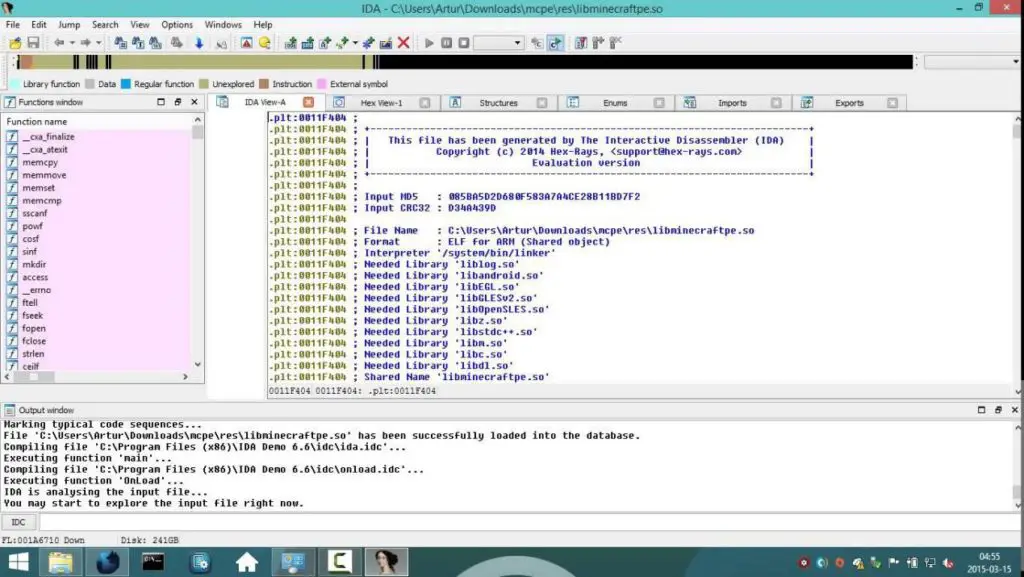
2) IDA
A multi-processor debugger, this tool works easily on different platforms such as Windows, Linux, Mac OS, etc. It provides easy analysis of hostile code, validation of COTS, etc. This software is widely preferred by experts due to its ability to provide vulnerability searches.
3) Androguard
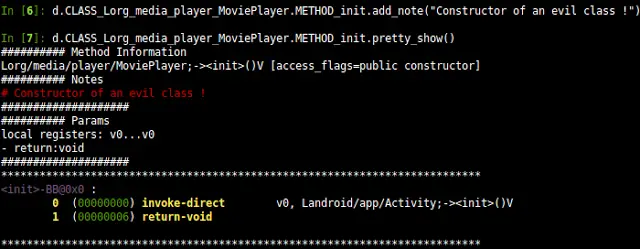
This tool is Python-based and supports various android applications. This tool is used to map various formats such as DEX/APK/AXML, etc. into Python objects. It is used in decompilation and modification of DEX/ODX/APK formats. It also helps in the transformation of binary XML of Android into classic XML.
4) DotPeeK
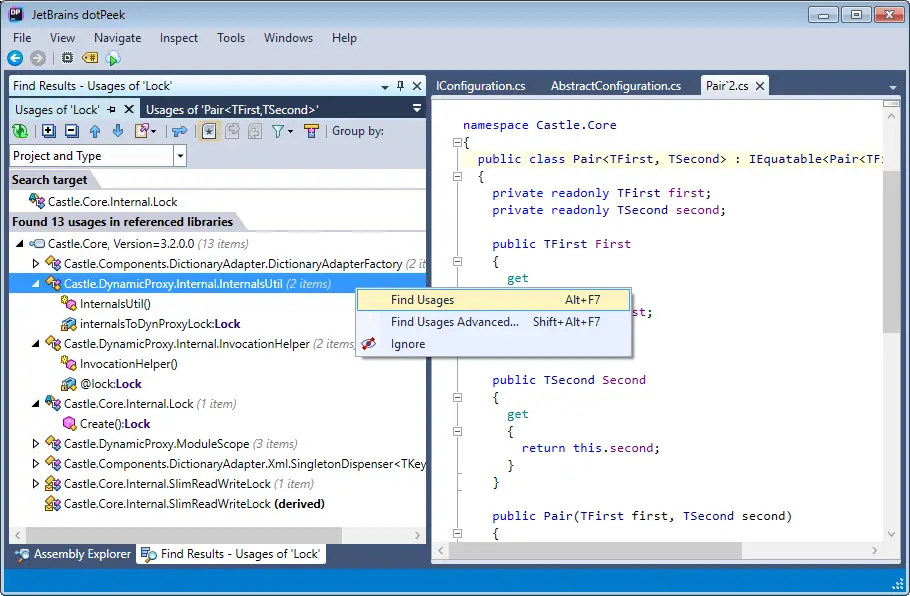
It is freely available bundled decompiler. It is used to decompile .NET assembly code to its equivalent IL or C# code. A popular standalone tool, it is known to support formats such as .dll, .exe, etc.
5) Dex2Jar
It is an API designed to read Dalvik executable formats. It supports Android as well as Java .class files. It is used to read dex instructions and then convert it into ASM format.
6) diStorm3
An easy-to-use tool, this tool disassembles instructions in different modes such as 16, 32 and 64-bit modes & is fast in disassembling the library. It depends widely on the C library and can be easily used in embedded as well as Kernel modules.
7) edb-Debugger
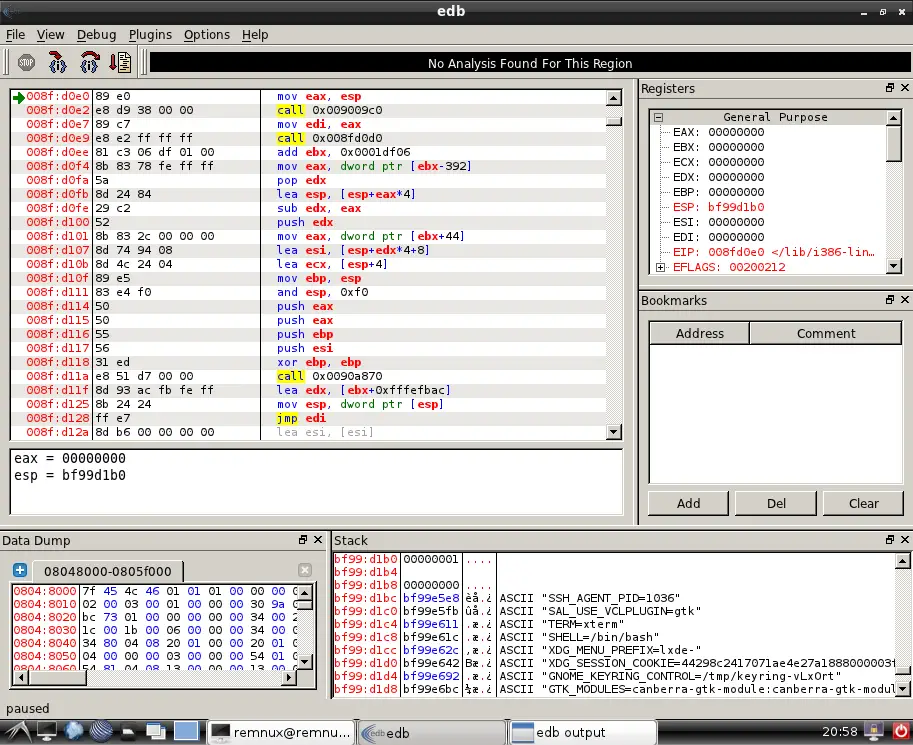
This tool works well on Linux and provides various debugging operations like step-into, run, break, etc. It offers the analysts to implement the debugging core in the form of a plugin to have drop-in replacements and address the inspections effectively. Memory regions and easily be viewed or dumped using this debugger whose sole goal is to offer modularity.
8) De4dot
It is an open-source .NET based deobfuscator that was written in C#. it tries to restore a packed assembly to almost original assembly. Using this tool, obfuscations like string encryption can be restored completely. It removes the proxy methods and is known to decrypt the strings either statically or dynamically.
9) Valgrind
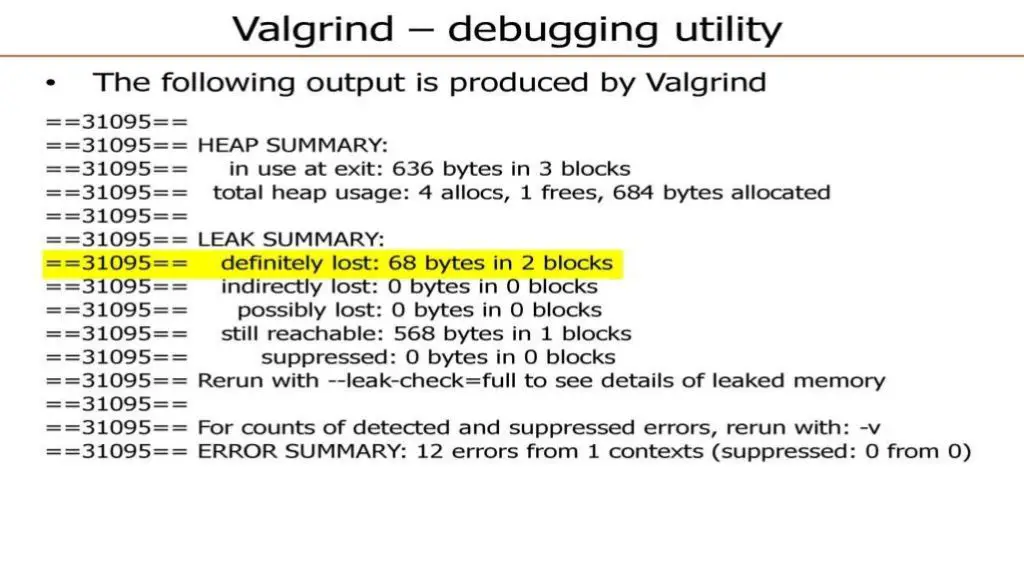
This tool is especially used for debugging the Linux programs. It is very useful in identifying the threading bugs and perform detailed profiling of the system thus enabling the programs to become stable. It can also be utilized to build new tools.
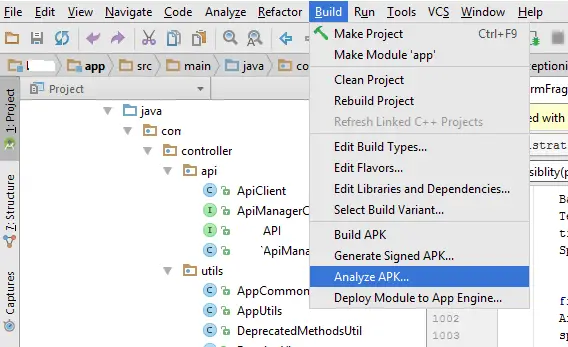
10) Apktool
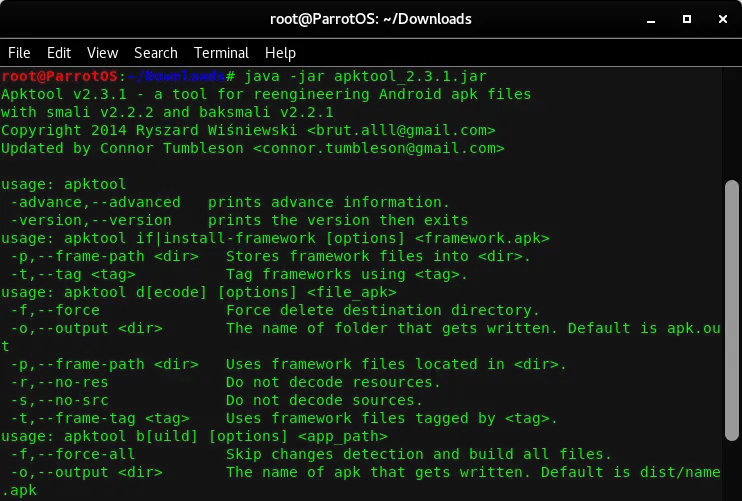
This tool helps to decode the resources to their nearly original form. After this process, those resources are recreated by making a few adjustments. It has got project-based file-structure that allows debugging of codes step by step. It also makes the app functioning easier.