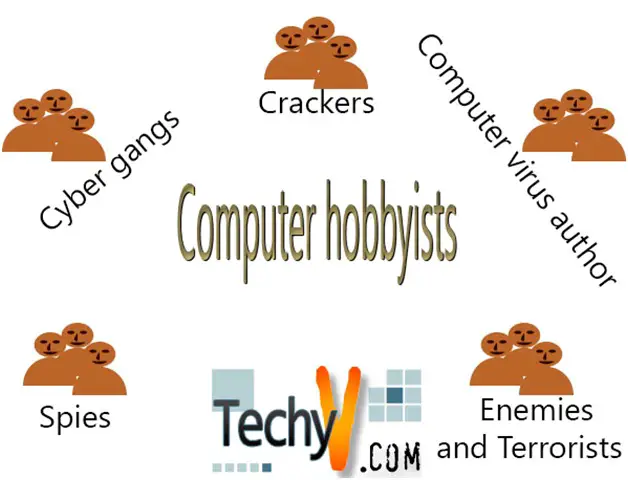
Computer hobbyists
The most common intruders of computer systems are the computer hobbyists and computer experts. They view unauthorized access as an irresistible intellectual game. Computer hobbyists are mostly known as “intruders”, but this term is very wide. There are various types of computer hobbyists and include intruders as their commonly known computer hobbyists.
They push computer systems to their limits. They perform experiments to programs so as to discover other unmentioned features and capabilities that are not found in the system’s manuals. Intruders modify computer systems to know their maximum performance, track down all potential weaknesses and loopholes in a system’s security. When intruders attempt unauthorized access, they hardly damage data from the system. They subscribe to an unwritten code of conduct known as the intruder’s ethic that forbids the damage of data because unauthorized access to them is usually intellectual diversion. Their other motives are ego gratification, building individual reputation, and also modifying prowess.
Crackers – these are types of computer hobbyists that are obsessed with gaining access to highly secured computer systems. Like hackers, they also do not intend to destroy data or steal assets. Crackers form communities, with a pecking order in terms of their reputation for cracking as well as frequency, sophistication, and virulence of their attacks. For most of the crackers, unauthorized access is a form of computer addiction. After gaining access, they document their feats by often leaving their calling cards or a message to the system they accessed.
Cyber gangs – they bring crackers together by means of the internet and also physical meeting; this is done to reinforce their immature and often destructive aims.
Computer virus author – A computer virus resembles a living virus. Like real virus, it has a host and develops to make copies of itself. Computer virus authors are mostly crackers and hackers. They are pros who offer their services to companies that hope to use their expertise to shore up their computer system’s defenses. This is known as ethical hacking.
Other computer intruders other than computer hobbyists include:
Spies – corporate computer systems contain a lot of information of interest to competitors, such as product development plans, customer’s details, product specification, and also strategic plans. These cause a rise in corporate espionage. Espionage threat goes beyond national borders. Spies get help from hackers and crackers. Spies can be ex-employees who have created trap doors that enable them to access the company’s computers without detection after they have left the company and joined another.
Enemies and Terrorists – they use information technologies to corrupt or destroy an enemy’s information, and industrial infrastructure. These attacks include electronic warfare, network warfare, and structural sabotage. Electronic warfare includes using electronic devices to damage computer systems. Network warfare uses hacker-like attacks on the nation’s network infrastructure; such as electronic banking. Structural sabotage includes using attacks on information systems that support major infrastructure in a nation. Information warfare is inevitable and is giving rise to information terrorism.
A lot is always at stake due to computer intruders, and breaches of computer security can be costly.