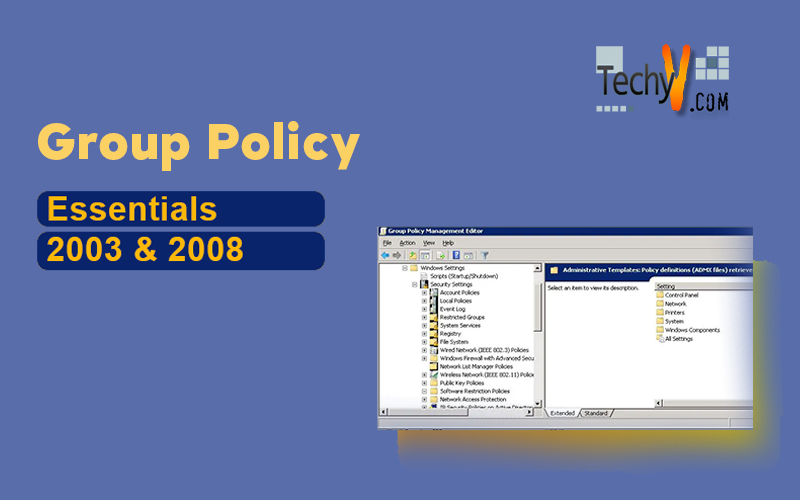
Group Policy Essentials
Group Policy provides a convenient and effective way to manage computer and user settings. With Group Policy, you can manage settings for thousands of users or computers in the same way that you manage settings for one user or computer and without ever leaving your desk. Group Policy is a set of rules that you can apply to help you manage users and computers.
Group Policy is a twofold idea. First, without an Active Directory, there’s one and only one Group Policy available, and that lives on the local Windows 7, Vista, Windows XP or Windows 2000 workstation. Officially, this is called a Local Policy, but it still resides under the umbrella of the concept of Group Policy.
Evolution of Group Policy from Windows 2000-to-Windows 2008 R2
Group Policy settings and reliability have changed tremendously since they were first introduced in Windows 2000 Server. In the Windows 2000 Server version, Group Policy Objects (GPOs) lacked many features and basically were not as resilient to network changes and many of the advanced functions just did not work. With Windows XP and Windows Server 2003, many features were fixed and new settings were introduced. With Windows Server 2008 and Windows Vista, many of the pain points realized in the previous versions were resolved and the infrastructure was in many ways rebuilt from the ground up.
With the release of Windows Server 2008 Group Policy preferences increases, a set of more than 20 Group Policy extensions that expanded the range of configurable settings within a Group Policy object (GPO).One major change in Server 2008 R2 and Windows 7, is by taking the first tentative steps toward automating Group Policy management using Power Shell. The rest of what you’ll find new in the latest Windows release is mostly updates to existing policy areas, some additional Windows components under Group Policy management, and some improvements to Group Policy preferences.
Highlights of Windows 2008 R2 Group Policy
Administrative Template Changes
A new ADMX format and the Central Store were introduced in Windows Vista. The ADMX format provides better multi language support; the Central Store took old ADM files out of the SYSVOL part of every GPO. With Server 2008 R2 and Windows 7, the greatest change in this area is the addition of yet more Administrative Template settings (300 or more). One of the more subtle changes to Administrative Templates is a modified ADMX schema that now supports two new registry value types: REG_MULTI_SZ and REG_QWORD. Previously, you couldn’t use Administrative Templates to modify these two value types.
Unified Administrative Templates UI in Windows Server 2008 R2
Power Shell Support
Microsoft added support for running Power Shell scripts within per-machine or per-user scripts policy and provided a set of 25 Power Shell cmdlets for Power Shell 2.0 that supports many of the operations you can perform within Group Policy Management Console (GPMC).
When you create a new startup script or logon script in GPE, you’ll see a new tab. As Figure 3 shows, you can now add Power Shell scripts to your scripts policy and control whether the scripts run before or after non-Power Shell scripts as shown below.
Figure below shows Server 2008 R2’s and Windows 7’s new Administrative Template policies
A full list of cmdlets exposed in the new module, called Group Policy, that Ships with the Remote Server Administration Tools (RSAT) feature in Server 2008 R2 and Windows 7 is available
New Policy–Enabled Features
Most of the new policies relate to security settings, but a few minor updates have been made to Group Policy preferences as well. We will start with the new
Group Policy preferences
• Support for managing the new Power Plans for power management that were introduced in Vista. These are now available in addition to Power Options and Power Schemes. Power Plans require that the client receiving them is running at least Vista.
• Updated Scheduled Tasks preferences now support the newer Task Scheduler that shipped with Server 2008 and beyond, as well as Vista. This new Task Scheduler supports many more options than Windows 2003’s and XP’s Task Scheduler. In addition, Microsoft added Immediate Tasks for Vista and beyond, which lets you create a one-time scheduled task that runs as soon as the policy processes.
• Addition of Internet Explorer (IE) 8 in the Internet Settings preferences, which lets you now configure options specific to IE 8.
New Security Policies
The biggest new addition in the area of Group Policy–based security policy is the Application Control Policies or AppLocker. These policies are found under Computer ConfigurationWindows Settings Security SettingsApplication Control Policies. Essentially, this is a significant upgrade to the old Software Restriction Policies (SRPs) which are still supported in Server 2008 R2 and Windows 7 that let you control which applications can execute on your Windows systems.
Specifically, AppLocker lets you create application white lists and blacklists to explicitly allow or deny a particular application or set of applications to execute based on a set of criteria you specify. A major difference between what’s available in AppLocker and SRPs is that you now have more flexible rules for defining applications. As below Figure shows, for example, you can create rules by software publisher, application name, and version information held within the file.
You can also create rules for controlling script execution, which wasn’t explicitly supported in earlier Windows versions. Also, for each type of rule you create, you can enforce the rule or just work in audit mode. In audit mode, whenever a rule is hit by an application, the result is logged to the client rather than blocking or allowing that application.
Advanced Audit Policy
Another security-related feature that you’ll find in Server 2008 R2 and Windows 7 is a much more granular auditing infrastructure. If you look under Computer ConfigurationWindows SettingsSecurity SettingsAdvanced Audit Policy Configuration, you’ll see 10 different auditing categories that you can now tweak to control exactly which types of events generate security audits on Server 2008 R2 or Windows 7 systems. This new granularity, of course, is exposed only in these newest OS versions, but the fact that it’s manageable via Group Policy is a good thing.
Network List Policies
One of the new security policies is the ability to control network lists. By default, when Server 2008 R2, Windows 7, or Vista systems find new networks, whether public wireless networks or corporate LAN, a user is prompted to indicate the type of network it is (e.g., public, domain, home). But by using Network List Policies in Group Policy, you can now pre configure how particular networks behave and which zone they should be shunted into when a user finds them. You can also control the icons and the names of the networks that appear to the user. The only downside to using this policy area for pre configuring wireless access points is that you need to know the name of the WAP ahead of time to configure all the various options. But this policy area is still a welcome addition for controlling users who frequently roam between networks.
Name Resolution Policy
The last new policy area, although not strictly a security policy (it’s found under Computer Configuration Windows SettingsName Resolution Policy in GPE), lets you control DNS Security Extensions (DNSSEC) and Microsoft Direct Access DNS configurations on a per-DNS domain name basis. For example, you can configure which features of DNSSEC are used for a given client talking to its DNS server, or which DNS and proxy servers a client connecting to your network via Direct-Access will use. Although not used by all shops, this feature is handy to have in Group Policy if you’re rolling out Direct-Access to your mobile users.
Creation and Linking of GPO
The most functional and useful tool provided to create and manage Active Directory group policies is the Group Policy Management Console (GMPC). The GPMC was introduced after the release of Windows Server 2003; the functionality included with different operating systems produces different options and resulting operations when creating and managing Active Directory group policies. When we create a GPO that can be used in Active Directory, two things happen: we create some brand-new entries within Active Directory, and we automatically create some brand-new files within our Domain Controllers. Collectively, these items make one GPO.
You can think of Active Directory as having three major levels:
+ Site
+ Domain
+ OU
Using Group Policy you can simply enable or disable a policy to tweak a registry value or other setting, and the change will apply once Group Policy is refreshed.
When you expand the Forest node, you see the following nodes:
- Domains provide access to the policy settings, for domains in the forest which are being administered. If you expand a domain, you can access Default.
- Domain Policy, the Domain Controllers OU and the related Default Domain Controllers Policy and GPOs defined in the domain.
- Sites Provide access to the policy settings for sites in the related forest. Sites are hidden by default.
- Group Policy Modeling provides access to the Group Policy Modeling Wizard, which helps you plan policy deployment and simulate settings for testing purposes.
- Group Policy Results provides access to the Group Policy Results Wizard. For each domain to which you are connected
The GPMC has one main job: to provide you with a Group Policy–centric view of all you control. All the OUs that you see in Active Directory Users and Computers are visible in the GPMC. With GPMC there is no way to “view” the users, computers, contacts, and such. When you drill down into an OU inside the GPMC, you’ll see but one thing: the GPOs that affect the objects inside the OU.
Creating and Linking GPOs
GPMC allows you to create and link GPOs on a selected domain, site, or OU. When you create and link a GPO to a site, domain, or OU, the GPO is applied to the user and computer objects in that site, domain, or OU according to the Active Directory options governing inheritance, the precedence order of GPOs, and other settings.
Creating and Linking GPOs for OUs
To create an OU in the GPMC, follow these steps:
1. Start the GPMC by clicking Start, Programs or All Programs, Administrative Tools, and then Group Policy Management Console. Or type gpmc.msc at a command prompt.
2. Expand the entry for the forest you want to work with, and then expand the related Domains node by double-clicking it.
3. Right-click the domain in which you want to create the OU, and then select New Organizational Unit.
4. In the New Organizational Unit dialog box, type a descriptive name for the OU and then click OK. As seen from the below figure an OU, Techno is created.
From the above we can see that under GPO object container we have created Techno GPO and the display link in this location is TechnoEncyclopedia.com.
Creating and Then Linking a GPO for an OU
To create a GPO for an OU and then link it separately, complete the following
Steps:
1. Start the GPMC by clicking Start, Programs or All Programs, Administrative Tools, and then Group Policy Management Console. Or type gpmc.msc at a command prompt.
2. Expand the entry for the forest you want to work with, and then expand the related Domains node by double-clicking it.
3. Right-click Group Policy Objects, and then Select New. In the New GPO dialog box, type a descriptive name for the new GPO and then click OK.
4. The new GPO is now listed in the Group Policy Objects container. Right-click the GPO, and then choose Edit.
5. In the Group Policy Object Editor, configure the necessary policy settings and then close the Group Policy Object Editor.
6. In the GPMC, expand the Domains node and select the OU you want to work with. In the right pane, the Linked Group Policy Objects tab shows the GPOs that are currently linked to the selected OU (if any).
7. Right-click the OU to which you want to link the GPO, and then select Link an Existing GPO. Use the Select GPO dialog box to select the GPO to which you want to link, and then click OK.
8. The GPO is now linked to the OU. In the right pane, the Linked Group Policy Objects tab should show the linked GPO as well
Group Policy of Major Categories Group Policy Category
Group Policy of Major Categories
| Group Policy
Category |
Where in Group
Policy Interface |
Which Operating
Systems Support It |
| Administrative
Templates (also known as Registry Settings) |
User or Computer à Policies
à Administrative Templates |
Windows 2000+ |
| Security Settings | Computer or User Configuration
à Policies à Windows Settings à Security Settings |
Windows 2000+ |
| Wired Network
(802.3) Settings |
Computer Configuration
Policies à Windows Settings Security Settings à Wired Network (IEEE 802.3) Policies |
Windows Vista+ only |
| Wireless Network
(802.11) Settings |
Computer Configuration à
Policies à Windows Settings à Security Settings à Wireless Network (IEEE 802.11) Policies |
Windows XP and Windows
Vista+ (set independently) |
| Scripts | Computer Configuration à
Policies à Windows Settings Scripts (Startup/ Shutdown) and Policies à Windows Settings à Script (Logon/Logoff) |
|
| Group Policy Software
Installation (also known as Application Management) |
Computer or User Configuration
à Policies à Software Settings |
Windows 2000+ |
| Offline Files | Computer or User Configuration
à Policies à Administrative Templates à Network à Offline Files |
Different Group Policy
“moving parts” to make this technology work in Vista+ and Windows Server 2008 than in previous operating systems; feature available in Windows 2000 and later. |
| Group Policy
Preference Extensions |
Computer or User Configuration
à Preferences (not available in local policies, only domain policies) |
Group Policy Preference
Extensions built in to Windows Server 2008 and Windows 7, but are an additional download and installation for Windows XP and Windows Vista; not supported on Windows 2000 machines |
| Internet Explorer
User Accelerators |
Windows 7+ |