Archive
Lease Lines vs. MPLS: Which is Best for Optimum Network Connectivity?
In this column, we will tackle two major forms of network connectivity: the Leased Lines and the MPLS. The fundamental concepts for both Leased line and MPLS technologies are used to connect multiple pisions in order to facilitate access and speed up data transfers greatly, especially for large type of organizations. Here are some fundamental ways on how connectivity performs on a given task. Lease Line Communication It is a circuit that provides full time connection to a network for data and voice communications. It can be used for telephone communications, send... Read moreThe ABCs of LAN and Fiber Optic Cables: Which Performs Better?
As remote network connections between computers continue to increase in popularity in the home and business world, you have two main options when determining what type of media is the best for your needs; LAN cables or fiber optic cables. Which type you’ll need is determined by your computing needs. In this article, we’ll discuss the differences between the two. What is a LAN Cable? LAN cables, or local area connection cables, are used to connect a large number of workstations in a given space, such as an office or... Read moreAcer Timeline X 3830TG Review
Acer America has released new, second generation, beautiful series known as Timeline. Acer is one of the most popular laptop companies. This company was founded in 1976. Since 2000, it focused on the new technologies and basic computing, its price is reasonable that is why it is rapidly growing in fame. New Acer TimelineX is available in 3 sizes; 13.3 inch 3830TG, a 14-inch 4830TG and 15.6-inch 5830TG. Acer 3830TG 13.3 inch had always dotted a modern ice blue, black and silver color scheme, but these days only ice blue is available in the market. Its... Read moreTablet PCs vs. Laptops: How is Tablet Different from a Laptop?
Laptops and tablet PCs serve the same purpose. Both of them run completely on operating system and both are fully portable. Both the gadgets run similar kinds of programs and applications. Nevertheless, there are numerous other things about tablet PCs and laptops as well which are as follows: Keyboards:
While you are considering a tablet PC's keyboard, a physical presence of a keyboard does not exist. As an alternative, they make use of an integrated application program that is useful in typing on-screen.... Read more
Keyboards:
While you are considering a tablet PC's keyboard, a physical presence of a keyboard does not exist. As an alternative, they make use of an integrated application program that is useful in typing on-screen.... Read more
The New PowerShell in a Nutshell
Microsoft Windows and Microsoft DOS components and hardware’s used in personal computers always includes an interface program which is a command line tool in all there releases. Most common are the cmd.exe and command.com, the command.com usually refers to systems relying on Ms-Dos and in even the new Windows 9X. The cmd.exe on the other hand, normally comes with operating systems in the Windows NT family. Basically, these are interpreters of simple command line. For more complex strings of commands, separate application consoles are needed. These mentioned interpreters are considered shells that are like... Read moreHow to Configure VMware Virtual Network
Configuring VMware Virtual Network In this article, we will cover virtual networking components that VMware provides and explore how we will use various network configurations on VMware workstations. Virtual Networks: VMware workstation provides the following types of virtual networks:- Bridged Network: This network model uses host computer physical adapter to connect the virtual machine to a network. Since it uses host computer adapter, the virtual machine can be visible to the other systems on the network and can communicate to other virtual machines.
- Network Address Translation (NAT): This model uses the host IP and MAC address... Read more
What is Kerberos and How Does it Work?
Kerberos is protocol software that is used in the authentication of communication among the computers connected in a network. It works by prompting computers connected to the same network to provide their identity. This ensures that each user operates in a secure mode, preventing unauthorized access to data. Kerberos is mostly used on the client to server type of networking, and it ensures that the client and server are experiencing equal authentication.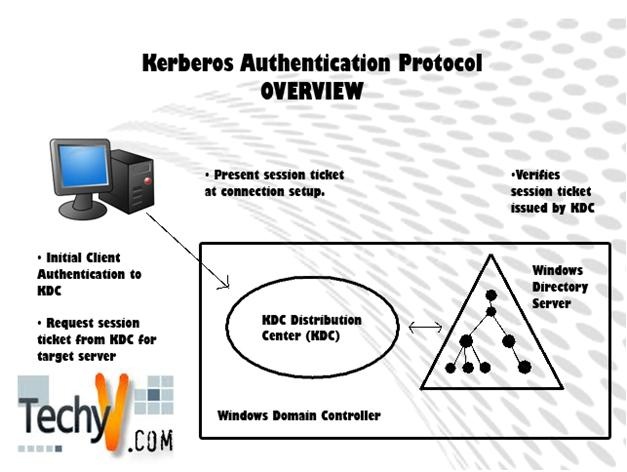
ISO 9001 Certification: Who Uses it and Why?
ISO 9001, an internationally accepted standard for quality management in business. It belongs to the family of ISO 9000 quality standards wherein it was established and is revised periodically by the International Standardization Organization. All the ISO 9000 standards are administered by international certification and accreditation bodies where ISO 9001 is among the most important standards in this category. It has been specially designed so that it may be applied to any service, product, or process anywhere around the globe. ISO 9001 applies particularly to those processes which create and manage the... Read moreMANAGING NETWORK PROTECTION AND SPEED WITH MICROSOFT’S ISA SERVER
The ISA or Internet Security and Acceleration Server (presently called Microsoft Forefront Threat Management Gateway) is the most up-to-date protection solution of Microsoft. It is intended to protect the computer or computer network from any software that is designed to access and manipulate any information without the owner’s approval. This is referred to as malware and has been identified to cause delay in accessing a particular website.
Mac OS X Lion by Apple
With the advancement in technology, Apple has launched OS X Lion with a lot of new features. OS X Lion has 240 main features. It is only available in the Mac App Store. This article will discuss the brilliant features OS X Lion comes with.
 OS X Lion comes up with a great new full screen mode that can manage all your applications in a single full screen. No more messing up with a lot of single screens cramped on your desktop. You can enjoy all... Read more
OS X Lion comes up with a great new full screen mode that can manage all your applications in a single full screen. No more messing up with a lot of single screens cramped on your desktop. You can enjoy all... Read more











