Domain Name System (DNS) encryption has become an essential aspect of secure web browsing in recent years. Unencrypted DNS traffic allows third parties to easily view what websites a user visits and collect browsing data. Encrypting DNS queries prevents this type of surveillance and protects user privacy. This article outlines ten leading protocols and services incorporating DNS encryption to enable secure web access. As background, the DNS matches domain names that humans can understand to machine-readable IP addresses. When a user types a web address into a browser, a DNS lookup retrieves the correct IP address to connect to. Typically, DNS queries happen unencrypted, allowing network observers to collect, analyze, censor, and modify traffic. DNS encryption protocols establish an encrypted session so lookups remain private. The sections below provide an overview comparison of 10 leading DNS encryption solutions for secure web browsing. While protocol specifics like cipher suites differ, fundamentally these all act to encrypt DNS queries in transit and obscure what sites a user visits.
1. DNSCrypt
First proposed in 2011, DNSCrypt transparently encrypts communications between a DNS client and server. It uses the high-speed, low-resource consumption Curve25519 and Salsa20 cryptographic functions. DNSCrypt connections start with an initial handshake to establish shared keys. Queries after that handshake are transmitted encrypted. Many public DNSCrypt server options exist. Selecting different servers prevents tracking by a single provider. DNSCrypt simplifies encrypted DNS for clients. However, provider servers must support DNSCrypt, limiting compatibility. As an older protocol without widespread native client adoption, options remain narrower compared to DoT and DoH.
2. DNS-over-TLS (DoT)
Standardized in 2016, DNS-over-TLS uses the same security protocol as HTTPS. As the name suggests, DoT incorporates Transport Layer Security (TLS) version 1.2 or higher to secure DNS sessions. This well-established system means excellent cross-platform compatibility. DoT only requires simple software upgrades to enable since it still uses the native DNS ports. However, session management does add some workload for DNS servers.
3. DNS-over-HTTPS (DoH)
Very similarly, DNS-over-HTTPS also runs DNS traffic inside the HTTPS encryption protocol using TLS. This leverages existing HTTPS hardware infrastructure and policies for efficient scaling. DoH formats DNS queries as regular HTTPS requests, trading off a very slight increase in bandwidth needs for blending into normal web traffic. Support continues improving across clients and devices.

4. DNS-over-QUIC (DoQ)
Representing a new IETF draft standard as of 2021, DNS-over-QUIC (DoQ) transmits DNS messages through the emergent QUIC transport protocol. Primarily designed by Google, QUIC incorporates cutting-edge encryption and optimization mechanisms. As an evolution of HTTP/2 and TLS 1.3, QUIC aims to reduce latency while enhancing security and reliability. Early data shows that DoQ significantly outperforms both DoT and DoH for resolution speed. However, DoQ currently lacks widespread software support pending final standardization. But given QUIC inclusion across leading web platforms, the adoption of DNS-over-QUIC should accelerate to match continuing QUIC growth.

5. NextDNS
As a reputable DNS encryption service launched in 2016, NextDNS operates over 150 high-performance Anycast resolvers implementing DNSCrypt, DoH, and DoT. This cloud-based platform offers a user-friendly setup across devices with fine-grained filtering controls backed by threat intelligence. NextDNS defaults to DoH connectivity with a fallback to DNSCrypt or DoT depending on client capabilities. For no added cost, NextDNS provides vital network security protections like phishing prevention and blocking of ads, trackers, and malware. Subscriptions add functionality around custom filtering, analytics, audit logs, and configuration management. With strong security and ease of use, NextDNS suits both individuals and organizations.

6. AdGuardDNS
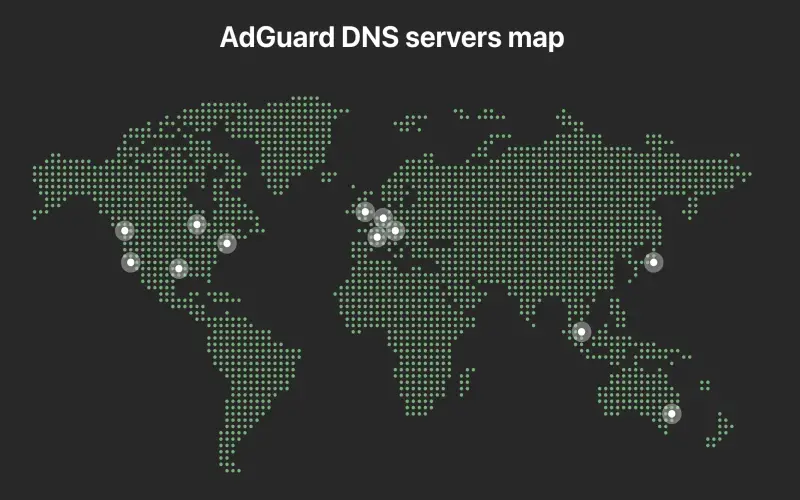
AdGuard DNS debuted in 2016 as a core component of the popular AdGuard ad and tracker-blocking software. Available at no charge, AdGuard DNS resolvers located globally now handle over 300 million queries daily via DNSCrypt and DoH protocols. Users benefit from the removal of ads, phishing sites, malware, and other threats during DNS resolution. AdGuard also rejects domain hijacking and enforces HTTPS for enabled sites. As a private DNS provider based in Cyprus, AdGuard does not record or share any personal data with third parties. Performance remains competitive despite expansive filtering capabilities. Individuals can conveniently boost privacy through AdGuard DNS alongside other solutions like VPNs.
7. Quad9
As a non-profit public DNS service launched in 2017, Quad9 emphasizes cybersecurity and privacy with a foundation of DNS-over-TLS encryption. Over 165 global PoPs adhere to a stringent no-logs policy while blocking threats identified from various intelligence sources. Available to use at no cost, Quad9 supports both DoT and DNSCrypt transports for authentication and encryption along with the DNSSEC protocol to prevent DNS spoofing. Users gain real-time protection against malware, phishing, botnets, and exploit kits.

8. Cloudflare
Since launching its public DNS service in 2018, Cloudflare has rapidly become a highly popular choice for fast and private DNS leveraging both DoH and DoT. Their massive network of 250+ locations powered by smart traffic routing results in a stellar performance for over 250 million daily queries. Cloudflare 1.1.1.1 app integrations enable one-click setup of encrypted DNS across most devices. While Cloudflare collects minimal analytics, its strict no-logs policy ensures user privacy along with threat blocking. Optional malware filtering via 1.1.1.2 and 1.1.1.3 addresses provides added security. Support for the latest web protocols like QUIC and TLS 1.3 demonstrates Cloudflare’s emphasis on DNS performance and encryption. For these reasons, Cloudflare DNS now ranks as a top internet encryption solution.

9. Pi-hole
As an open-source software package first released in 2016, Pi-hole takes a distinct localized approach to encrypted DNS via network-wide ad blocking. Users install Pi-hole onto Raspberry Pi devices or Docker containers acting as the DNS resolver and filter for the entire network. This allows all clients to benefit from the removal of ads, tracking, and telemetry metadata during DNS requests without any client configuration. Encrypted DNS protocols like DNS-over-TLS can further secure communications between Pi-hole and upstream resolvers. However, Pi-hole itself does not transmit encrypted DNS traffic by default from local clients. Still, tech-savvy home networking enthusiasts can build out a Pi-hole solution to filter DNS queries and transport encryption for maximal privacy across smart devices.

10. Unbound
Providing recursive and caching DNS functionality, Unbound has served as an open-source DNS resolver since 2007 with a focus on security and correctness. While raw Unbound traffic remains unencrypted, system administrators commonly run Unbound with DNS-over-TLS or DNS-over-HTTPS plus DNSSEC support to handle enterprise-wide encrypted DNS needs. This on-premise local resolver model grants organizations maximum control and privacy while bypassing public DNS infrastructure.